For Education
Connect and Protect Students on Any Device
One platform keeps students on task and safe
across all devices.
For Business
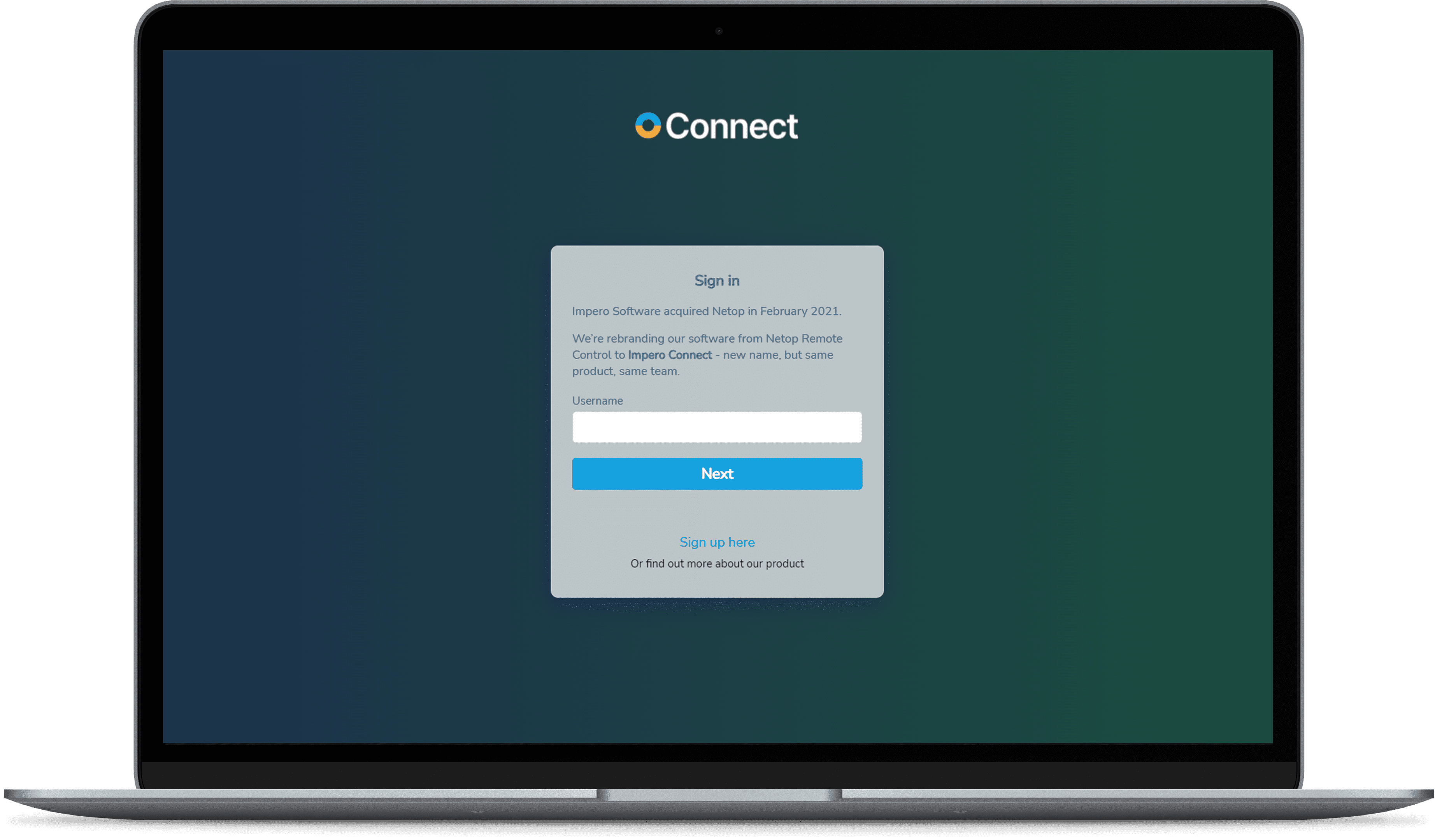
The Most Secure Remote Access Solution
Connect with confidence to ATM, POS and other
sensitive devices.
What We Offer Our Customers
Secure Remote Access
The majority of network data breaches occur through unsecured remote access points. That's why some of the world's largest institutions turn to Impero for secure remote access solutions that provide agile access without increasing network vulnerability.
Remote Access - Heathcare
Keep patient data secure while ensuring your healthcare IoT environment stays up and running. Impero Connect remote access solutions work with specialized devices while meeting rigorous healthcare security standards.
Remote Access - Retail
With support for a variety of operating systems including Toshiba TCx™ Sky & 4690, Impero Connect delivers the efficiency, flexibility, and security you need to manage your retail environment, all in one, consolidated tool.
Remote Access - Banking
Financial institutions rely on Impero Connect to reduce travel costs, save time, and lower overhead when supporting end users, maintaining ATMs and meeting SLAs. Our integrated security tools protect your IT environment as well as customer data, helping you stay PCI compliant and exceed your financial institution's security standards.
Remote Access - Manufacturing
Impero Connect provides fast, secure and reliable remote control of current and legacy production devices.
Classroom Management
Got Windows? Chromebooks? Macs? IPads? Android? Impero Classroom can handle all of it, delivering real-time monitoring in or out of the classroom.
Student Safety
Keep students safe and detect issues early with contextual keyword alerts and a full chronology of every student's safety history.
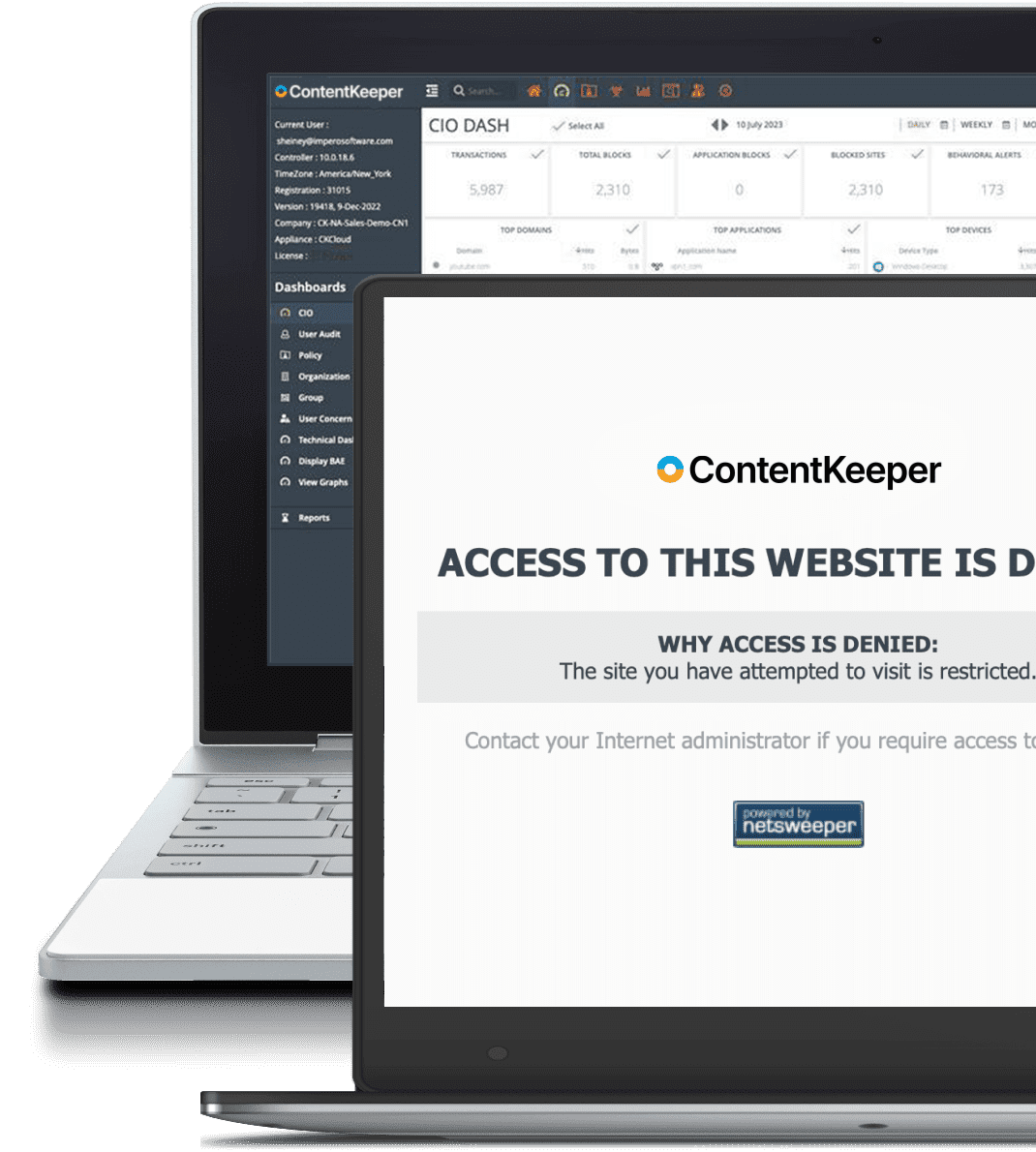
Filtering
Stop malicious attacks, suspicious activity, and rogue applications with powerful web filtering for all platforms, operating systems, and BYOD devices.
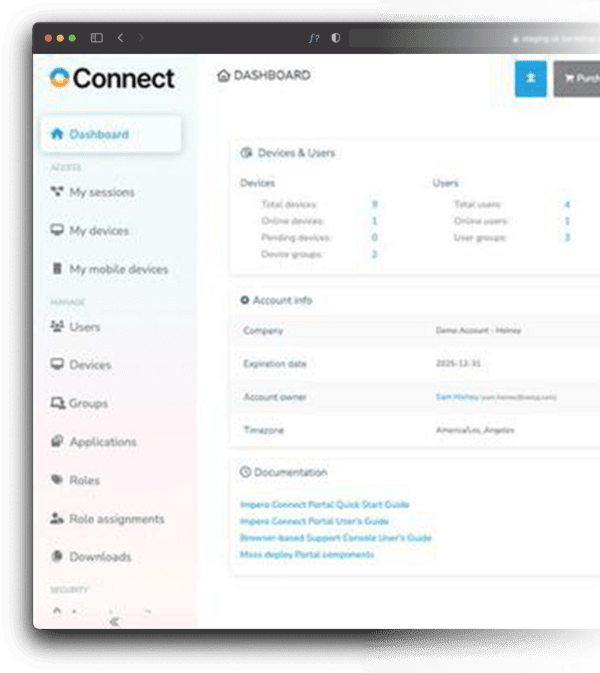
Secure Remote Access
Get through your ticket backlog with remote access that doesn't leave you exposed to hackers.
Secure Remote Access
The majority of network data breaches occur through unsecured remote access points. That's why some of the world's largest institutions turn to Impero for secure remote access solutions that provide agile access without increasing network vulnerability.
Remote Access - Healthcare
Keep patient data secure while ensuring your healthcare IoT environment stays up and running. Impero Connect remote access solutions work with specialized devices while meeting rigorous healthcare security standards.
Remote Access - Retail
With support for a variety of operating systems including Toshiba TCx™ Sky & 4690, Impero Connect delivers the efficiency, flexibility, and security you need to manage your retail environment, all in one, consolidated tool.
Remote Access - Banking
Financial institutions rely on Impero Connect to reduce travel costs, save time, and lower overhead when supporting end users, maintaining ATMs and meeting SLAs. Our integrated security tools protect your IT environment as well as customer data, helping you stay PCI compliant and exceed your financial institution's security standards.
Remote Access - Manufacturing
Impero Connect provides fast, secure and reliable remote control of current and legacy production devices.
Classroom Management
Got Windows? Chromebooks? Macs? IPads? Android? Impero Classroom can handle all of it, delivering real-time monitoring in or out of the classroom.
Student Safety
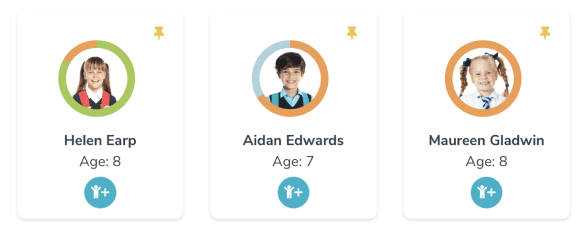
Keep students safe and detect issues early with contextual keyword alerts and a full chronology of every student's safety history.
Filtering

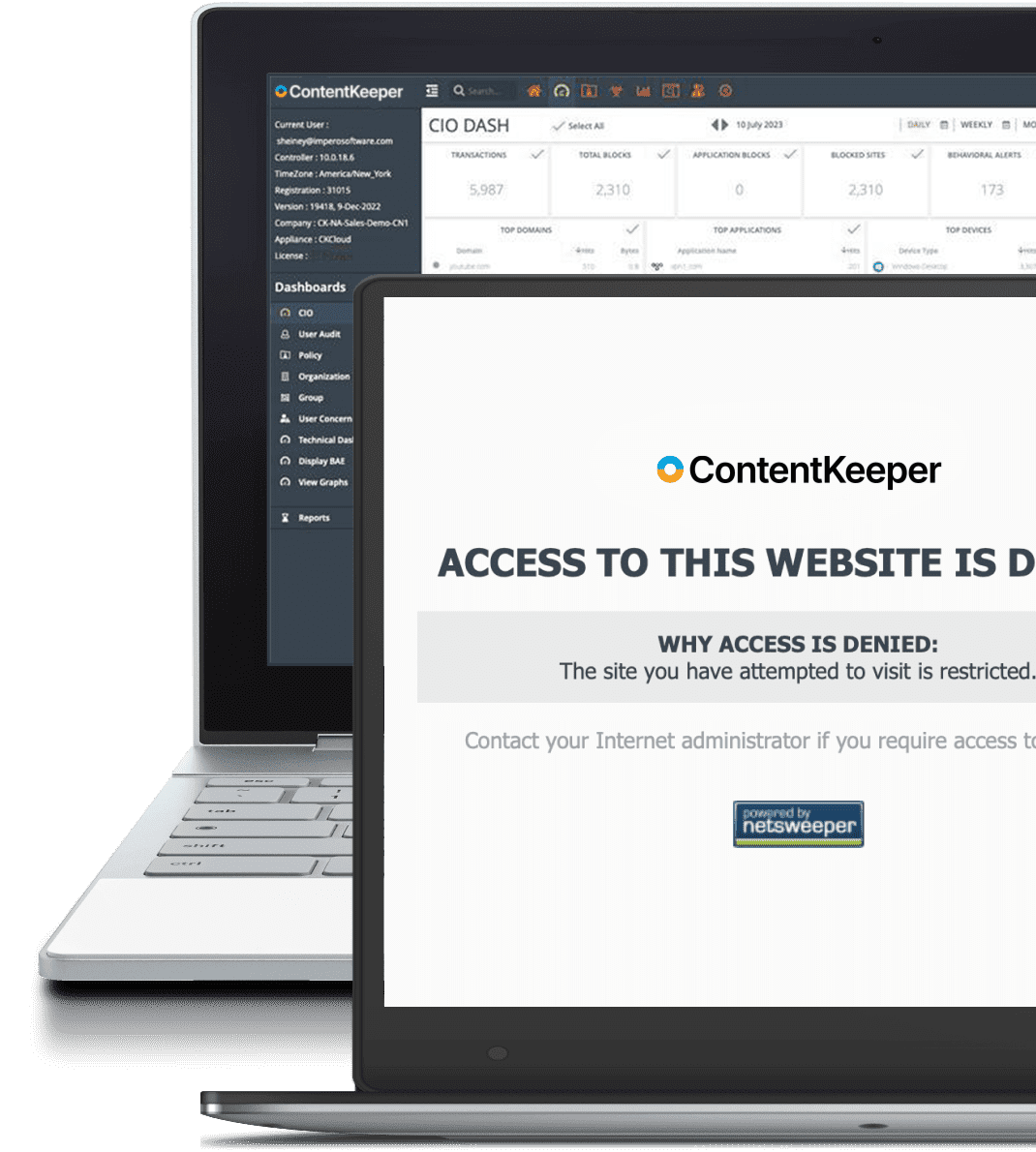
Stop malicious attacks, suspicious activity, and rogue applications with powerful web filtering for all platforms, operating systems, and BYOD devices.
Secure Remote Access
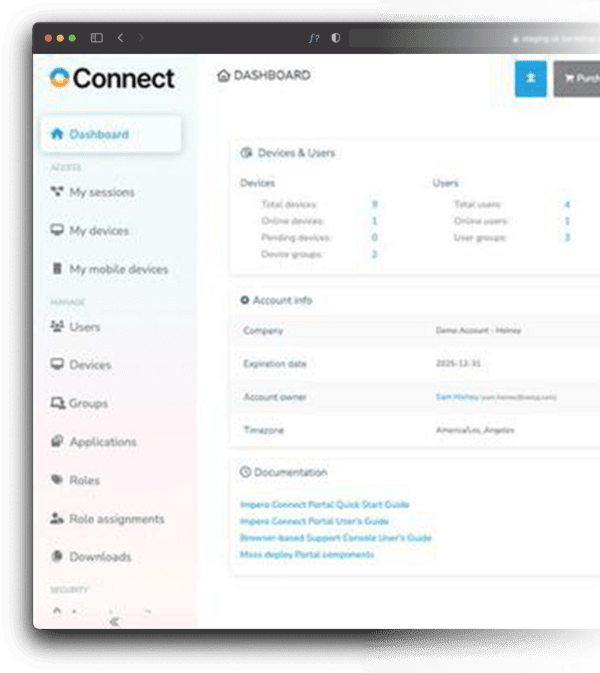
Get through your ticket backlog with remote access that doesn't leave you exposed to hackers.
Why Our Customers Choose Us
Security
Our solutions keep your users and data safe from known threats and inadvertent breaches from unauthorized user activity.
Compatibility
Only Impero provides solutions with native support for a broad range of operating systems.
Deployment Options
Cloud-based, on-prem or hybrid - Impero solutions can be configured to meet your unique needs.
Insights
Get a holistic view, of your students, your school, or your network access without hassling with spreadsheets.
Efficient
Our solutions are cross-platform and modular to make your work simpler and easier.
Support
24x7 support with superior customer satisfaction.
Why Our Customers Choose Us
Security
Our solutions keep your users and data safe from known threats and inadvertent breaches from unauthorized user activity.
Compatibility
Only Impero provides solutions with native support for a broad range of operating systems.
Deployment Options
Cloud-based, on-prem or hybrid - Impero solution can be configured to meet your unique needs.
Insights
Get a holistic view, of your students, your school, or your network access without hassling with spreadsheets.
Efficient
Our solutions are cross-platform and modular to make your work simpler and easier.
Support
24x7 support with superior customer satisfaction.
"We find enormous value in Impero because it brings the functionality and information of technology down to the people who use it."
Longview ISD
"Overall Impero is a great multipurpose tool for IT and classroom management in the school. It is a great support tool for me as an IT admin and an effective classroom monitoring/management tool for our computer lab teachers."
Fox Creek High School
"The most important aspect of the software is that all concerns are in one place and can be viewed in chronological order. This helps staff to keep track of unfolding events, recognise when there needs to be an alert"
"As well as online safety and cyber bullying, it is useful to maintain a system of evidence and allow for a quick flagging system."
Annfield Plain Junior school
"Lessons can be taught knowing that the students are focused on the activity, and online distractions removed."
Alderman Peel High School
"Technology can be such a distraction and being able to lock the screens means that there is more engagement with the curriculum at the point it is needed. It's benefitting teaching and learning, not just safeguarding."
Jersey Offshore Establishment
"Following an evaluation phase of multiple remote maintenance solutions, we determined that only one of the standard products fulfilled our specifications. Impero Connect was the only solution providing us with a revision roof recording of each session. The new remote maintenance has also had apositive impact on the hospital's liquidity."
University Hospital Aachen (Uniklinik Aachen)
"Reducing time spent by employees on the road is a must, and Impero Connect's ability to do this makes it an essential technology partner in our ongoing green programs. The resources we save are making a huge impact on our bottom line"
Skanska
"Great response times when in remote control of a terminal and allows for connectivity into the company's active directory for a full view of users and devices accessible."
Walgreens Boots Alliance
"Fairly easy to use, very secure, self contained product that doesn't require any extra software or access rights on OS to function"
HSBC
Trusted By The Best